
Security
Van Buren v. United States — Oral Argument
The Supreme Court heard oral argument in Van Buren v. United States, a case concerning a statute of the Computer Fraud and Abuse Act (CFAA) and violations of terms of service agreements.
The technical heart: vulnerability research, disclosure, threat analysis, the craft of finding and fixing

Security
The Supreme Court heard oral argument in Van Buren v. United States, a case concerning a statute of the Computer Fraud and Abuse Act (CFAA) and violations of terms of service agreements.
Security
Security
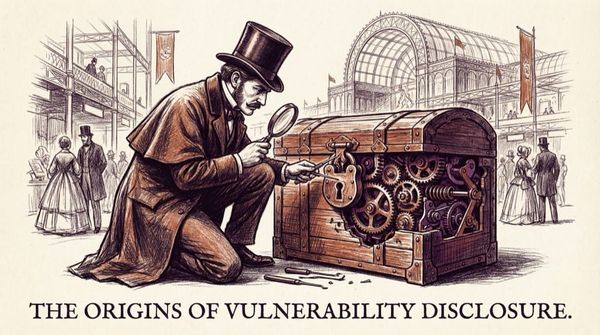
"What Hobbs had in mind was not the usual cajoling of a provincial bank into an upgrade, but exposing weaknesses in the British Empire itself by revealing the faults of one of Day and Newell’s competitors."
Security
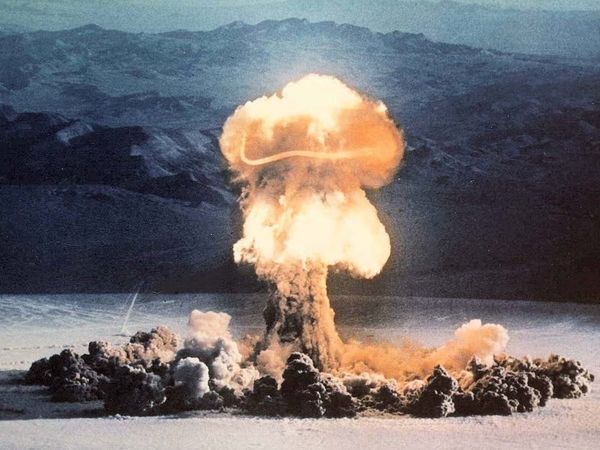
Props to Matt Ploessel for calling out this one... I'd not heard of a bounty around nuclear weapons until today.
Security
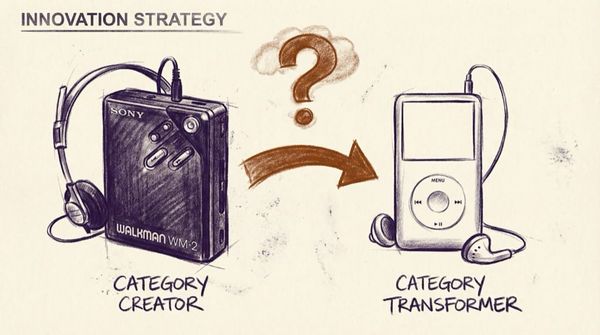
When the walkman was introduced, it created a category. It's brand also became the term of description for that category.
Security
Nth Country Experiment - Nuclear MuseumCould any country with the right knowledge and technology build a nuclear bomb? From May 1964 to April 1967, the Lawrence Radiation Laboratory (the predecessor to the Lawrence Livermore National Laboratories and the Lawrence Berkeley National Laboratory) set out to answer this question. The Laboratory
Security
7. Expect and plan for mistakes. Expect mistakes, and plan to capture and mitigate them quickly. After all, to err is human. Establishing a vulnerability disclosure and/or bug bounty program to engage hackers to continuously assess newly cut code is an effective and scalable way to achieve this. Casey
Security
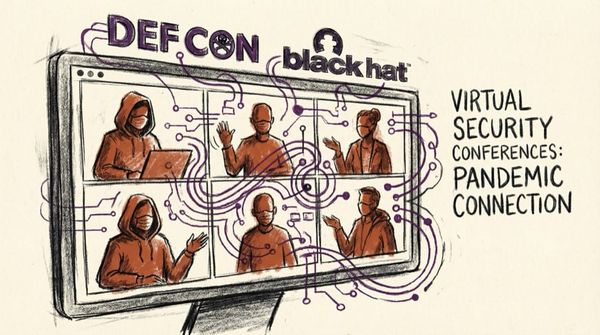
While it feels illegal to hang out with your friends right now, the pandemic is no match for the dedicated folks who unite for Black Hat and DEF CON every year. In 2020, both conferences are running virtually, highlighting the remarkable zeal with which security professionals and hackers continue to
Security
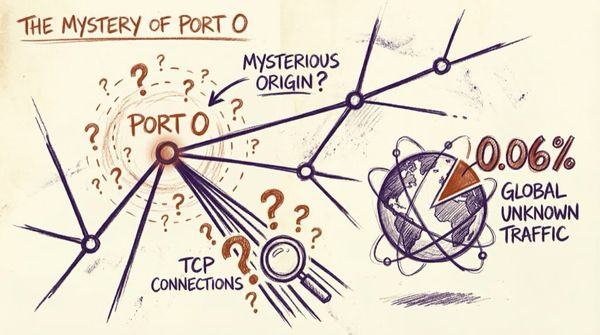
tl;dr: 0.06% of the publicly-addressable IPv4 space is listening to and responding on TCP Port 0. Why? idk…
Security
tl;dr: 0.06% of the publicly-addressable IPv4 space is listening to and responding on TCP Port 0. Why? idk... Note: Never interact with a computer system beyond your level of authorization (i.e. without getting permission first). Connecting for a TCP handshake is fine... It's how the

Security
I spend a lot of time looking at cybersecurity solutions and companies, partly on request, and partly because it always fascinates me to see people are attempting to solve big problems.

Security
2020: Chaos is a Ladder As 2020 comes to a close, I’ve started to see summaries of the year pop up, covering lessons learned from the year nobody saw coming… As years go, 2020 was full of those! While I wish I could go back in time and tell