A message to folks providing "free testing" at the moment
TLDR: If you’re performing any active, unsanctioned testing on healthcare systems: Please stop it. Don’t make their job any harder than it is right now.
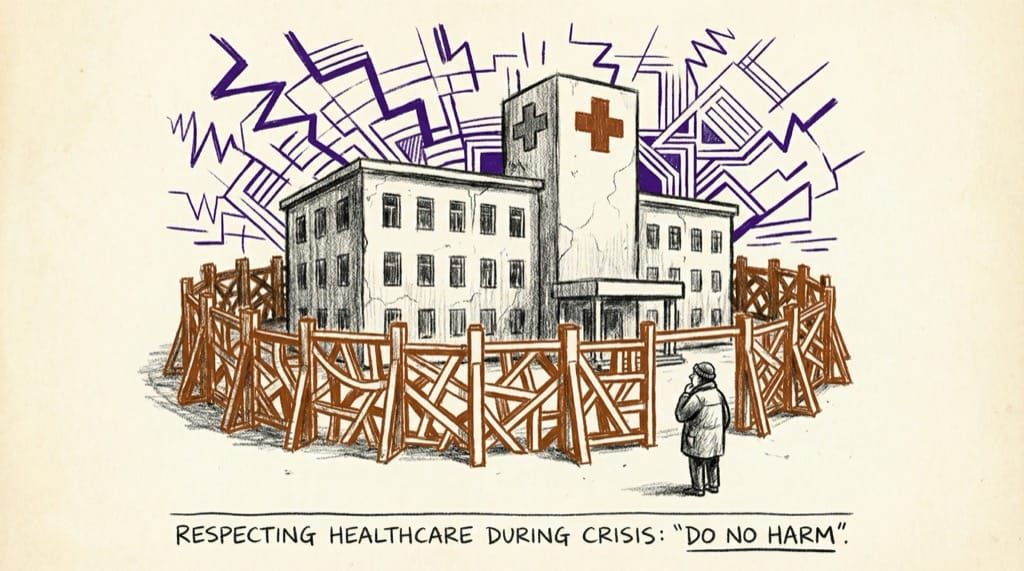
Free help is fantastic – especially in a crisis – and the response of the cybersecurity community jumping in to help on the cyber-side of COVID-19 has been incredible and heartwarming to be a part in and to observe.
Unfortunately, I’ve heard from a few places about upticks uptick in “pentest-like” activity from the Internet reported by healthcare organizations – ranging from hospitals, governing bodies, labs, EHRs, and doctors.
The problem is that on the receiving side it’s impossible (without having commissioned and planned to expect testing traffic) to distinguish between:
- Genuinely malicious recon activity,
- Well-meaning but unsanctioned bounty/vulnerability disclosure work, and
- The output of security vendor ambulance chasing (…pardon the pun).
Aside from dealing with the covid19 crisis itself, the blue teams, infrastructure teams, and governing critical infrastructure bodies around these orgs are on high-alert for bad behavior at the moment, and these activities are inadvertently sending a lot of people in Incident Response down rabbits holes
This wastes precious time.
TLDR: If you’re performing any active, unsanctioned testing on healthcare systems: Please stop it. Don’t make their job any harder than it is right now.

By doing so, you’ll help these organizations focus on threat mitigation, and you’ll probably help yourself avoid a loud knock on the front door down the line.