WTF is happening on tcp:0? 2020 edition — Update 1
tl;dr: 0.06% of the publicly-addressable IPv4 space is listening to and responding on TCP Port 0. Why? idk…
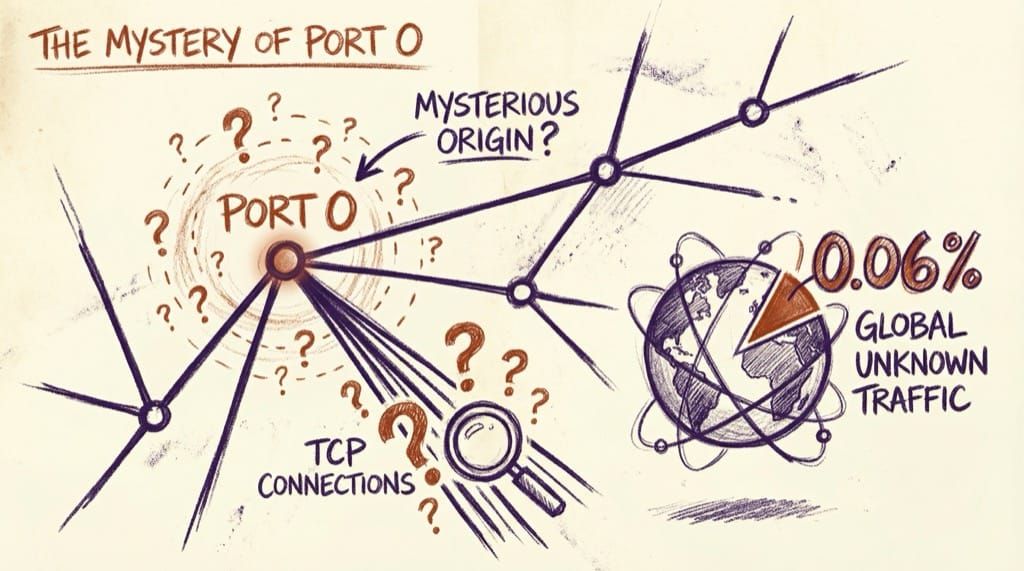
tl;dr: 0.06% of the publicly-addressable IPv4 space is listening to and responding on TCP Port 0. Why? idk…
Note: Never interact with a computer system beyond your level of authorization (i.e. without getting permission first). Connecting for a TCP handshake is fine… It’s how the Internet works. Doing stuff beyond that is left as an exercise for the reader and, again, don’t break the law as you do research (A strategy on how to exploit this phenomenon, stay legal, and possibly make some money is at the bottom of this post).
A few updates:
- A banner grab on a random sample using nmap produced a 5% hit-rate of a full handshake + information passed subsequent to the handshake.
- Some of the banners that were returned appeared to be services which were also present on other TCP ports (e.g. 443).
- There was some confusion about what configuration would respond positively to an nmap ping and if nmap knows the difference between an ICMP return and a TCP:0 return. Apparently it does.
- The hosts that didn’t return a banner all returned the nmap post state of “filtered”.