A few good cybersecurity companies
I spend a lot of time looking at cybersecurity solutions and companies, partly on request, and partly because it always fascinates me to see people are attempting to solve big problems.
A lot of has shifted in the attack surface, attacker behavior, and corporate and personal operational and IT processes over the past 6 months. This trend is likely to continue as the world oscillates between crisis-mode, recovery-mode, and attempted normalcy.
I spend a lot of time looking at cybersecurity solutions and companies, partly on request, and partly because it always fascinates me to see people are attempting to solve big problems. This post is unpaid, unsolicited, and spruiks of organizations that I think are nailing problem-spaces relevant to almost ALL organizations in 2020.
In general, there are a few things I look for in a good cybersecurity solution:
- Respect for the thesis, principals, and consistency of the founding team
- Design that “makes secure easy, and insecure obvious.”
- Clear messaging that addresses the pain they solve (vs. the solution they’ve created)
- A focus on stupidly happy customers through excellent product design and implementation
- A price point and structure that scales vertically and horizontally
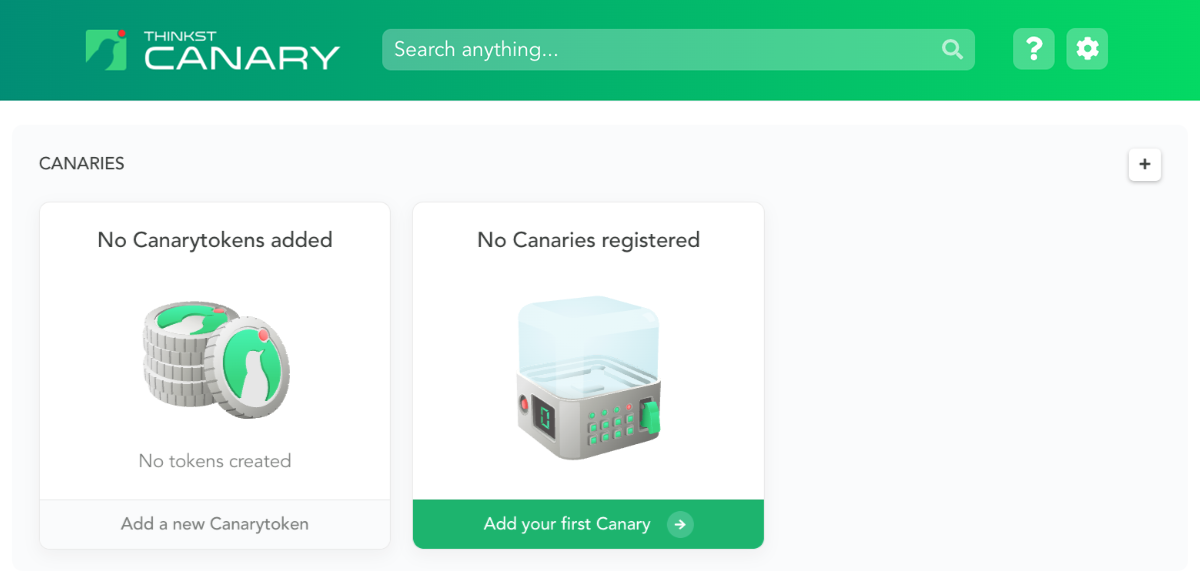
- Haroon Meer is one of my favorite cybersecurity strategists, but it’s the design and implementation of Thinkst Canary (both the honeypot and the canary tokens) that makes me a fan.
- Deception is a high-signal approach to correlating attacker behavior, and as somewhat of a strategist myself I think it’s still highly underrated
- Thiskst combines the beautiful, intuitive design of a technically sophisticated and oddball niche of cybersecurity with an accessible and straightforward pricing model
- Their flexibility of deployment in a hybrid corporate/work-from-home environment is a clear win for securing both in a cohesive way
- They’re bootstrapped, which is something I always admire in a successful organization (I think bootstrapping can be a stupid decision, and I also believe unnecessary fundraising can be a wrong choice too)
- They get bonus points for a vibrant, fun, and recognizable brand that focusses on creating STUPIDLY HAPPY CUSTOMERS
- Chad Loder is one of the founders of Rapid7 and has meaningfully disrupted cybersecurity for the better more than once
- Defensive cybersecurity only really works once the need to do it well is internalized by users within an organization, and Habitu8 is built around this idea
- Habitu8 does this by pairing very pragmatic and consumable explanation of security concepts with Hollywood-level production and communication
- It’s the kind of security awareness training users want to consume

- HD Moore is the fast-talking and even faster-thinking legend behind Metasploit. He’s another founder that I have profound respect for
- Rumble combines all of the tinkering and trickery of HD’s decades of pwning the internet into a tool that gives straightforward, fast, and comprehensive internal asset visibility
- It’s super easy to install and web-based for easy usage
- The network load it creates is quite low which, given the enormous amount of insight it generates and the speed it does so is remarkable from a technology standpoint
- You can down and use it at home for free, and I recommend it: It’s a little scary the first time you fire it up.
- Decentralization and message sovereignty for the division between “Church and State” is heating up as an essential consideration – both personally, and corporately
- Many apps and solutions attempt to solve this, including many that are bundled with phones… but Signal is independent, open-source for accountability, and works on a zero-knowledge and minimal metadata basis
- It’s the first solution I’ve seen that actually does all of this with a non-technical (think: Grandpa or Joe/Jane Internet), feature-driven user (think: younger folks or people who rely on rich messaging) into an E2E platform without an experience that requires a degree in rocket science.
- It’s far from that – Signal operates like just about any other messaging platform.
So, there you go – Casey’s unsolicited hot takes on stuff you should go try out.
Check them out, try their free stuff, consider it for yourself and your organization… and: Tweet me if you’ve got solutions you think are kicking ass in these same sorts of ways – I’d love to learn more!