Building
Techcrunch: Use ‘productive paranoia’ to build cybersecurity culture at your startup
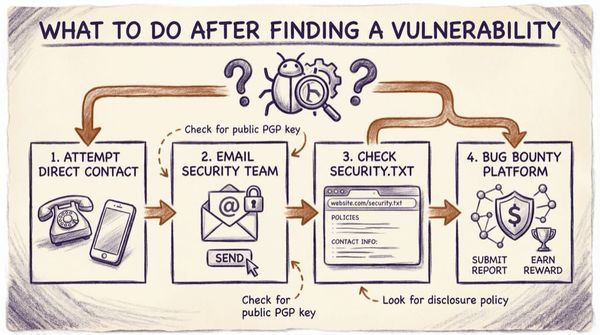
At TechCrunch Early Stage, we asked Casey Ellis, founder, chairman and chief technology officer at Bugcrowd, to share his ideas for how startups can improve their security posture.