Help! I've found a vulnerability. What now?
"You've just found a bug on a company's website. What are the first three to five things you'll try in order to establish contact with them?"
A question came up today on Twitter…
…which I was tagged in to answer:
I get asked this a LOT, and have a lot of people reach out to get help with getting vulnerability info into the right hands outside of existing customers of Bugcrowd, so I figured I’d knock out a quick post:
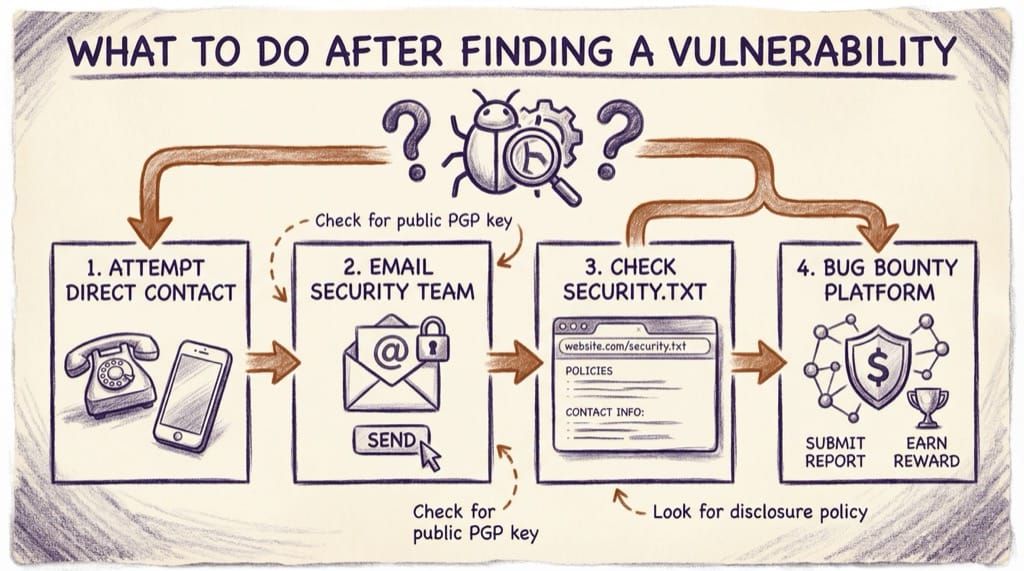
- Check their website /security page if there is one, their security.txt and the disclose.io List to see if they have a listed vulnerability disclosure policy and contact channel. If there is one, use it. If there isn’t, go to Step 2.
- IMPORTANT: Do a quick bit of Googling for any history of being nasty with researchers. If they have, it’ll probably be obvious. If it’s there, contact your local Computer Emergency Response Team (CERT) to provide a layer of protection and abstraction. If not, go to Step 3.
- Check LinkedIn for folks with Security, vulnerability management, or incident response in their title, and try hitting them up via LinkedIn or Twitter DM. DO NOT send vulnerability details over social networks. If this fails, go to Step 4.
- Ping someone in the vulnerability disclosure “Original Gangsters” crew and asking nicely for help making a connection. A little light OSINT will help you find someone who is experienced, connected, and can help. Never forget that you are interrupting them and asking for their time in this process… Politeness and gratitude go a long way, even though you’re already trying to do the right thing. If this fails, go to Step 5.
- Send high-level information about the nature of the vulnerability to security@domain, support@domain, and help@domain. At the same time, pass the full vulnerability details over to CERT.
I haven’t added the “Drop it on Pastebin” option here because, as always, that is an exercise left to the reader. It is not recommended from a legal, safety, and protecting your peer’s standpoint unless you REALLY know what you’re doing.