Security
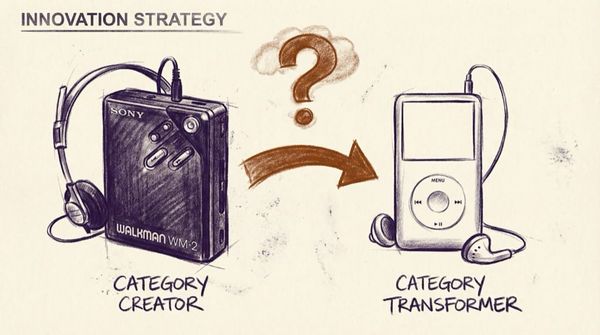
Are you making a Walkman? Or an iPod?
When the walkman was introduced, it created a category. It's brand also became the term of description for that category.
Processing experience into insight - retrospectives, lessons
Security
When the walkman was introduced, it created a category. It's brand also became the term of description for that category.
Building
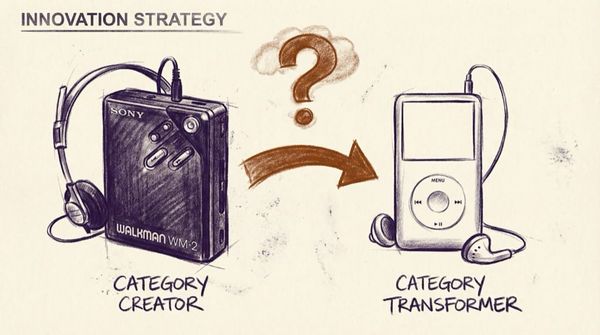
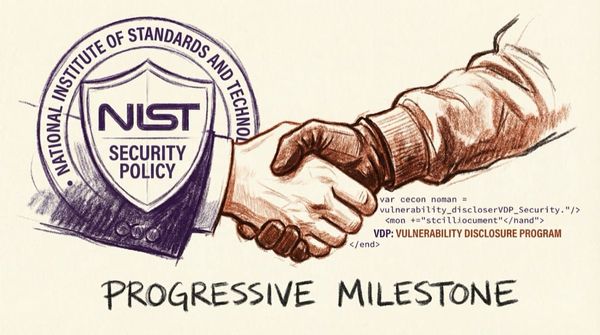
NIST SP 800-53 Revision 5 is yet another step towards the legitimization of the Internet’s Immune System. Everyone who has worked on legitimizing the work of good-faith hackers for the past 30 years or more can feel encouraged by this release.
Personal
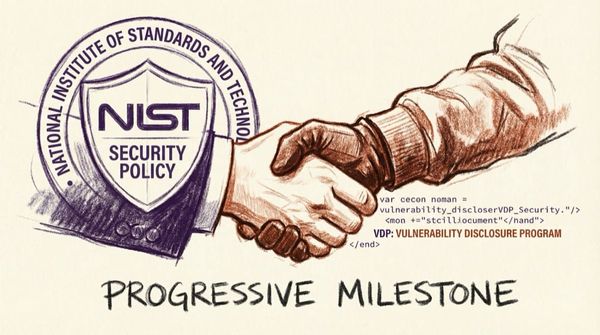
Seasoned experts get as much out of the “feet on the street” insights and energy of younger mentee as the mentee gets from their wisdom of the mentor.
Personal
I had a coach share this with me a little while back and it resonated - It's a valuable and simple framework, and a good set of questions to always be in a position to answer.

Building
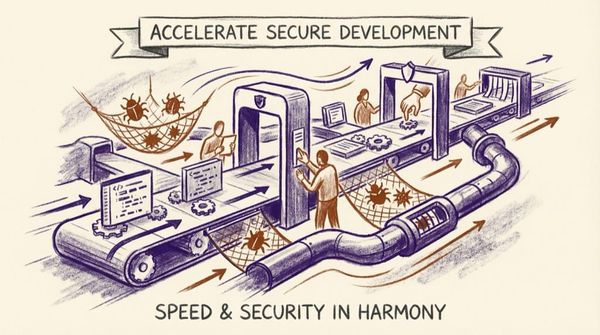
At TechCrunch Early Stage, we asked Casey Ellis, founder, chairman and chief technology officer at Bugcrowd, to share his ideas for how startups can improve their security posture.
Security
Nth Country Experiment - Nuclear MuseumCould any country with the right knowledge and technology build a nuclear bomb? From May 1964 to April 1967, the Lawrence Radiation Laboratory (the predecessor to the Lawrence Livermore National Laboratories and the Lawrence Berkeley National Laboratory) set out to answer this question. The Laboratory

Policy
We the undersigned cybersecurity companies and professionals write to express strong support for the IoT Cybersecurity Improvement Act (H.R. 1668). We respectfully urge you and your colleagues to support expedited passage of the bill before the end of the 116th Congress.

Building
Dear Director Krebs and CISA/DHS team, Thank you for the opportunity to comment on this Binding Operational Directive...
Security
7. Expect and plan for mistakes. Expect mistakes, and plan to capture and mitigate them quickly. After all, to err is human. Establishing a vulnerability disclosure and/or bug bounty program to engage hackers to continuously assess newly cut code is an effective and scalable way to achieve this. Casey
Policy
Earlier this week, the National Institute of Science and Technology (NIST) released Revision 5 of NIST Special Publication (800–53) Guidelines Security and Privacy Controls for Information Systems and Organizations. This revision makes a tremendous step toward bringing the role of good-faith security researchers (or, as they prefer to be
Policy
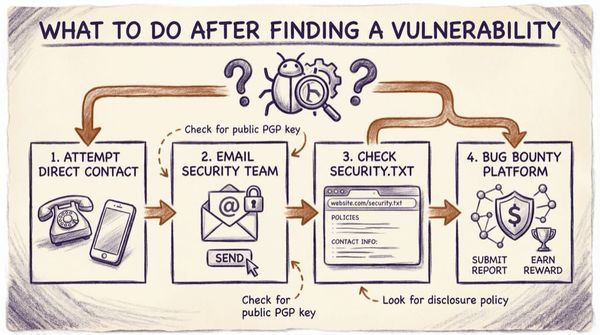
"You've just found a bug on a company's website. What are the first three to five things you'll try in order to establish contact with them?"

Policy
About 18 months ago, I sat in Capitol Hill with a bunch of other badasses including Matt Blaze, Kimber Dowsett, Jack Cable, Alexander Romero, Leonard Bailey, and others, and talked to voting machine manufacturers and US states.