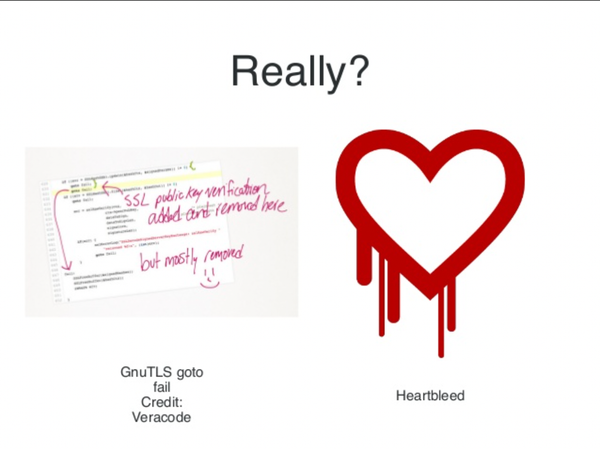
Security
Where the bloody hell were you — The Great 2020 COVID Bug-In
During Hacker Summer Camp, I was asked "where do you, uh, live now and stuff" a lot. Forgive this slightly indulgent post, but I wanted to blog a little bit of our story, and some of the thinking that went into executing our trans-pacific COVID bug-in back in 2020.




![[TRANSCRIPT] Threats that may have gone unnoticed by organizations during the pandemic](https://storage.ghost.io/c/ec/8a/ec8abb38-39b9-4422-95b9-695b2a5e652e/content/images/size/w600/2021/08/Screen-Shot-2021-08-28-at-9.34.21-PM.png)
![[TRANSCRIPT] Threat hunting in the age of work-from-home](https://storage.ghost.io/c/ec/8a/ec8abb38-39b9-4422-95b9-695b2a5e652e/content/images/size/w600/2021/08/Screen-Shot-2021-08-28-at-9.35.35-PM.png)